I think I have understood the concept of SSH tunneling. Tunneling is encapsulating one network protocol inside another. Consider the following scenario to understand. Lets say three computers A,B and C are connected in a network. B is allowed to connect to C but not A. How would A connect to C ? It can disguise as B and connect to C, right ? The disusing is called Tunneling, hiding or encapsulating.
A -> B -> C
Tunneling tools are available in market, the most readily available tool is ssh client. SSH client in the UNIX/Linux machines have capability to to do SSH tunneling, i.e, it provides feature to hide network traffic in SSH connections (tunnel). This is called SSH tunneling. SSH is secured connection, so the connection tunneled through it, is also secure.
SSH Tunneling is the most exploited method to hack networks. It is also used to by pass corporate firewalls. We can understand this in detail using below network diagram.

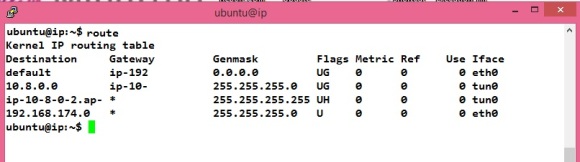
This is a typical network diagram, Corporate network is hidden behind the firewall. The firewall has rules – which allows/deny incoming and outgoing connection. Client, SSHHost, WebHost, DBHost are nodes which are running SSH Server, Web server and Database server respectively. All the nodes are connected with each other and accessible over the network ( or internet ).
Most corporate firewall allows outgoing connections at port:80, 443. These are port for web server and secured web (https). If some corporate user wants to connect to web server, it can connect, the firewall would allow http connection at port 80. But, if the user wants to connect to a database server (at port 1521) outside firewall, the firewall would deny the connection.
SSH (local) Tunneling can allow the corporate user to connect the Database server. All we have to do is to create a connection from a client (here Webshot) to SSHHost server.
Webhost $ ssh -L 443:DBHost:1521 sshuser@SSHhost.
This will create a connection from Webhost to SSHhost and it will create a tunnel from Webhost to DBhost as well. The tunnel is actually a server process on Webshost listening for incoming connection on port 443 and redirecting to DBhost. The firewall would think that the request is made on the port 443, but eventually it will be redirected to database server on port 1521. In this case the Webhost is called jump server.
SSH local tunneling can give access to servers behind the firewall. But, how can we access servers inside the corporate firewall. Lets assume we want to show a website available in corporate intranet to outside world. This can be achieved using SSH reverse tunneling. For SSH reverse tunneling to work, the the firewall should allow to connect to a ssh server outside firewall (port 22 should be allowed on the Firewall). Create a ssh connection from a computer (localhost) inside the firewall.
corporate computer # ssh -R 9999:localhost:80 sshuser@SSHHost
This would create a ssh connection from the machine inside, corporate to the SSHHost server. Additionally it would create a server on SSHHost at the port 9999. Incoming connection to SSHHost on port 9999 would be redirected to corporate computer port 80. We can access the website hosted on corporate computer (localhost) from outside. Hit http://SSHhost:9999 in the web browser on the client. it will open website hosted within intranet.
The SSH Server on SSHHost should have “GatewayPorts yes” in the file /etc/ssh/sshd_config. The computer we are targeting with in the firewall should also have “GatewayPorts yes”.
The concept of tunneling is old and not well documented. It took me some time to understand it. Feel free to ask questions and share your comments.
 ESP-01
ESP-01